This blog post was written as part of the Digital Forensics Fellowship by one of the 2022-2023 Fellows.
The forensic analysis of smartphones was one of the critical pieces of evidence in The Pegasus Project. Traces left by Pegasus spyware on the phones infected with it allowed the survivors of this intrusive surveillance to become aware of the egregious breach of their privacy.
The forensic tools and process used by Amnesty International’s Security Lab has been open-sourced as the Mobile Verification Toolkit (MVT). This software allows anyone to check a back-up of their own smartphone for indicators of spyware infection.
As human right defenders, being able to do forensic analysis on our own tools is empowering. It allows us to maintain a good understanding of our level of security and confidentiality. A streamlined process also allows us to help those around us in a timely manner.
In order to scan a smartphone with MVT, the technologist has to obtain a back-up of the smartphone. The MVT docs contain multiple ways to obtain a backup for an iOS device and an Android one.
A person doing a forensic analysis of a smartphone would then need to run MVT on the back-up of the smartphone. MVT can be run from the command line and outputs results directly into the console. The person doing the forensic analysis will obtain a number of files, generated by MVT, containing the results of the analysis.
The process of running analysis from the command line may be familiar to those who are used to running command in terminal applications, but it can also feel alienating to those who work predominantly with software with a graphical user interface.

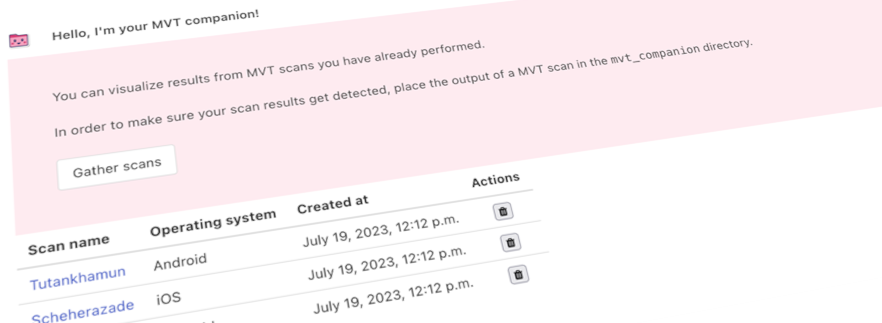
I have developed MVT-Companion, an open-source software project, during my Fellowship with the Amnesty International Security Lab. It is a web app that can be used to visualise information from MVT forensic scans inside the browser.
The goal of MVT-Companion is to allow anyone to view forensic scan results from MVT and understand, at a glance, whether the devices might have been targeted with spyware. This is an ongoing open-source software project, and more developments are expected in the upcoming months. MVT-Companion also accepts Pull Requests, Issues and feature requests.
MVT-Companion is Docker-based. It is a Django application that uses a PostgreSQL database to store results. The repository contains a Makefile that makes spinning up and developing MVT-Companion easy.
The Docker image for MVT-Companion also contains mvt itself and androidqf. One of the long-term goals of the project is to allow users to perform smartphone backups and forensic scans from the Docker containers. In this way, MVT-Companion could become a containerized toolbox for forensic analysis.

The MVT-Companion GitHub repo contains information on how to run the application, and how to import forensic results. For iOS, the app also displays the installed applications.
MVT-Companion is an ongoing project. More information extracted from the forensic analysis will be added to it. I envision adding the following modules to it:
● The ability to also view installed APKs and the permissions that are granted to them;
● The ability to search through the APKs and iOS applications installed across devices and see all devices which have a certain application installed;
I welcome Feature Requests (as Pull Requests) for this project. I am interested in what people would like to be able to see, from the results that MVT outputs.
All information provided by MVT and MVT-Companion, related to indicators of compromise on a device, are not definitive proof that a device is currently being monitored using spyware. These are tools for conducting an investigation, but, ultimately, you are doing the forensics.